Key Takeaways:
- The public nature of the blockchain introduces privacy concerns about data-privacy for retail and institutional users
- Layer-2 solutions, especially zero-knowledge technology, can provide a trustless way to maintain privacy
- However, user privacy remains a distant milestone in the roadmap for most L2 offerings
- While privacy-solutions for corporate blockchain use are multiplying, the landscape for retail-focused solutions remains limited
- There are technical challenges associated with deploying smart-contracts using zero-knowledge validation techniques
- The fragmentation of L2 offerings, especially from the same L2 providers, puts the ball in the court of dApp developers to ensure retail user privacy
I recently posted about the various privacy concerns for end-users emerging from the public nature of blockchain technology. These concerns also extend to businesses that are wary of putting sensitive/proprietary data on the public block.
Layer-2 solutions such as Polygon Technology (MATIC), Offchain Labs (Arbitrum), Matter Labs (zkSync), OP Labs (Optimistic Ethereum), StarkWare (StarkEx), etc. might be the answer.
What are Layer-2 Solutions?
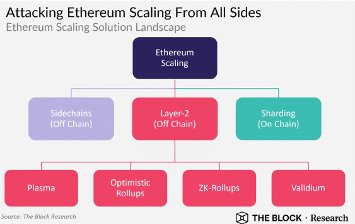
Layer-2 solutions are essentially scaling mechanisms for a Layer-1 protocol (think ETH), allowing for cheaper and faster transactions. So far popular Layer-2 solutions have been Polygon Technology, Optimism, and Loopring, and are generally adopted by users looking to mitigate Ethereum’s transaction costs and network congestion.
Most people who have transacted through Polygon, however, are actually transacting through a side-chain (e.g. Sandbox, Decentraland, QuickSwap users) rather than a true L2 solution (although Polygon’s suite of products offers these). The key difference between a sidechain and an L2 is that while bridge contracts on sidechains assume that transactions executed on the sidechain are valid, bridge contracts on L2s can verify transaction validity per ETH rules.
Layer 2 solutions are essentially a method whereby many transactions are (performed off the main-chain) rolled into a single bundle, and the bundle’s validity is then communicated to the L1 protocol. This significantly reduces the number of transactions the network has to process. Although most L2 solutions work by offloading transaction execution off the main-chain (Ethereum), the ways in which they are implemented vary — 1) Zero Knowledge Rollups, 2) Optimistic Rollups, 3) Validium/Plasma. The key difference between Rollups and Validium/Plasma is that the latter also offload data availability (in addition to transaction execution) from the underlying L1 platforms. While this can be valuable for protecting data privacy, the data stored off-chain does not have the same security framework as the underlying L1 protocol and can also create issues if the data goes offline.
Types of Rollups: Zero-Knowledge vs Optimism?
Optimistic Rollups (OPs) such as Arbitrum and Optimism work under the assumption that all transactions are valid and provide a one-week period to challenge that assumption, leading to delay in moving funds off-bridge. The data underlying the transaction bundles are kept on-chain and public.
Zero-Knowledge Rollups (ZKs) instead create validity proofs for bundled transactions that can be independently verified by the L1 network similarly reducing the number of transactions that need to be processed without the 1-week fund withdrawal delay. Theoretically, ZKs are cheaper and more scalable than OPs, but in practice, OPs tend to be cheaper since generating and verifying proofs is computationally intensive, and therefore time-consuming and costly.[1] However, the biggest barrier to ZK adoption is that the technology is not compatible with “with most decentralized applications,” which is why “70% of the Layer 2 market opted to adopt OP Rollup instead”.[2] Here compatibility simply refers to compatibility with EVM (Ethereum Virtual Machine) which creates a sandboxed environment to execute smart-contracts. At the moment, ZK rollups are mostly used for “exchanges and other apps that require simple payments,” rather than general purpose applications.”[3] An example of this is Loopring, which primarly provides DEX and Payments scaling solutions, and was recently tapped by GME to handle transactions for its NFT marketplace.
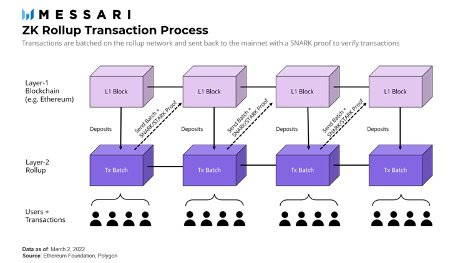
Vitalik Buterin, an Ethereum Co-Founder, notes that while “in the short term, optimistic rollups are likely to win out for general-purpose EVM computation and ZK rollups are likely to win out for simple payments, exchange and other application-specific use cases, but in the medium to long term ZK rollups will win out in all use cases as ZK-SNARK technology improves.”[4]
The future that Buterin imagines, may arrive sooner than expected with the development of a new general-purpose Zero-Knowledge proof scheme called “PlonK”.[5] Polygon Hermez and zkSync 2.0, currently deployed on testnets, will also provide zkEVMs which will be able to perform EVM-like computation in ZK rollups previously considered impossible. To put it simply, zkEVM is essentially an EVM (the sandbox where ETH smart contracts are executed) that executes smart contracts in a way that is compatible with zero-knowledge-proof computation.
What does this Technology Mean for Data Privacy?
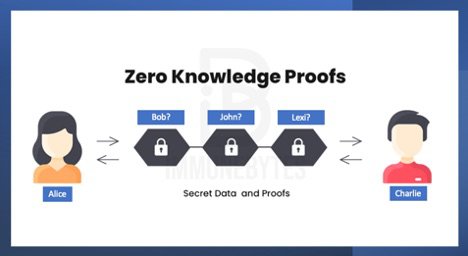
ZK Rollups, and the underlying ZK-Snark proof mechanism is often hailed as the privacy layer that a public blockchain like Ethereum requires.[6] The reason behind this is fairly straightforward — ZK proofs enable one party (the prover) to prove to another party (the verifier) that transactions are valid, without disclosing or conveying transaction information to prove their validity. However, since ZK Rollups require data availability on-chain, they are susceptible to privacy breaches, and most current solutions have prioritized scaling ZK rollups over building privacy.[7]
As an example, suppose that Alice submits a transaction paying Bob 1 ETH, and Bob submits a transaction paying Charlie 1 ETH, in quick succession. Later you verify a proof that Alice has 1 ETH less than before, Bob’s balance hasn’t changed, and Charlie has 1 ETH more than before.
While this does protect the intermediary’s privacy, i.e., since the ZK proof would not know if Alice paid Charlie directly, or whether Alice paid Bob who then paid Charlie, or any combination of intermediaries through whom payments were transferred, the start and end-points are still known.
Most current privacy-focused solutions utilize a hybrid of ZK proofs and either Validium/Plasma networks which take data availability off-chain, or Optimistic Rollups which reduce transaction costs.
One such example is Matter Labs’ zkPorter (useable in zkSync 2.0) which is a hybrid between a Validium and a ZK rollup. In zkSync 2.0, the L2 state will be divided into 2 sides: zkRollup with on-chain data availability and zkPorter with off-chain data availability.8 allowing for cheaper transactions, data privacy, flexibility, and L1 level security if so desired. Both parts will be composable and interoperable: contracts and accounts on the zkRollup side will be able to seamlessly interact with accounts on the zkPorter side, and vice versa, resulting in a 100x reduction in fees paid by zkPorter accounts. StarkWare’s Volition is a similar solution that lets users dynamically pick between ZK-Rollup & Validium. StarkWare’s has also released StarkNet Alpha on the Ethereum mainnet, an early, experimental scaling solution with ZK-Rollups that will be EVM comptabile, and add volition mode over the course of development. Similarly, Polygon’s Nightfall, developed in concert with EY is an Optimistic rollup enhanced by the privacy benefits of ZK cryptography.[9] The beta for Nightfall went live on May 17, 2022, and is aimed at corporate uses that will be legally and KYC-complaint. It is important to note, however, that even off-chain data is not completely private, since it is held by trusted 3rd-parties who know all user vault balances.[10] Although enabling privacy mechanisms is on the roadmap of many of these networks, they are currently yet to be implemented per my understanding.
One of the solutions proposed Buterin was the idea of “recursive proof ” which refers to the act of verifying another proof inside a proof, i.e. verifying another SNARK proof inside a SNARK proof.[11] This is a convenient, if technically challenging, compression technology that can improve efficiency and reduce privacy protection costs. It has the added benefit of not needing to delegate the user-data to trusted 3rd-parties which can be compromised.
Aztec, which launched its second iteration of its ZK-ZK Rollup, or in shorthand, ZK² last year is an application of recursive proofs. It is set to launch its Aztec Connect solution supporting cheap, private transactions on the Ethereum mainnet on June 6, 2022. Mystiko.Network, currently in testnets while it completes its audits, proposes a more elegant integrated into its software development kit or “privacy as an SDK” (PaaS), aiming solving multi-chain interoperability and privacy at once.[12] Meanwhile, Polygon, which has the most comprehensive suite of L2 solutions, aims to launch Polygon ID to offer on-chain verification and permissionless attestation that will be privacy first.[13]
Where Do We Go From Here?
As mentioned above, the majority of ZK proof and rollup solutions currently are not compatible with EVMs and cannot host a majority of dApp deployments. Meanwhile, zkEVM solutions like Polygon Hermez and zkSync 2.0, are prioritizing other features over privacy in their development roadmap. Furthermore, StarkWare’s StarkNet, when it does add Volition capabilities for off-chain data management, will need to rely on trusted 3rd-parties to ensure privacy. As such the landscape for user privacy is severely fragmented, and it is an open question if various offerings from L2 solutions will integrate with each other to provide all the available advantages of Ethereum scaling, lower transaction costs, and consumer privacy.
While it will be relatively straightforward for well-funded institutions to determine which L2 offerings to deploy on, retail DeFi, GameFi, and dApp users will have significant trouble determining which platforms best protect their privacy and at what scale. The ball is in the court of developers to create solutions that despite being KYC-complaint offer the best available privacy protections for their users, and are well-positioned to migrate their applications once better solutions become available.
References and Notes:
[1] Note that this is not always the case. Per-transaction on-chain gas costs can be lower if the transaction is only used to verify, and not to cause state changes, since the data can then be left out, whereas in an optimistic rollup it would need to be published in case it needs to be checked for a fraud-proof.
[2] https://vulcanpost.com/780967/huobi-zkevm-key-efficiency-ethereum-blockchain-platform-malaysia/
[3] https://limechain.tech/blog/optimistic-rollups-vs-zk-rollups/
[4] https://vitalik.ca/general/2021/01/05/rollup.html
[5] https://www.prnewswire.com/news-releases/huobi-research-institute-predicts-zkevm-will-inject-life-into-ethereum-301484516.html; See also Plonky2, a recursive SNARK that is 100x faster than existing alternatives and natively compatible with Ethereum. It combines PLONK and FRI for the best of STARKs, with fast proofs and no trusted setup, and the best of SNARKs, with support for recursion and low verification cost on Ethereum. https://blog.polygon.technology/introducing-plonky2/
[6] https://www.forbes.com/sites/samantharadocchia/2018/04/24/why-zk-snarks-are-crucial-for-blockchain-data-privacy/?sh=f400d8550f04; https://yourstory.com/the-decrypting-story/what-is-zk-proof-rollups-blockchain-ethereum-polygon-zero-knowledge/amp
[7] https://coinyuppie.com/why-do-we-need-on-chain-privacy-protection/ ;
[8] https://blog.matter-labs.io/zkporter-a-breakthrough-in-l2-scaling-ed5e48842fbf
[9] https://messari.io/article/polygon-a-multi-sided-approach-to-zk-scaling
[10]https://docs.starkware.co/starkex-v4/starkex-deep-dive/data-availability-modes
[11] https://vitalik.ca/general/2021/01/05/rollup.html
[12]https://www.coindesk.com/sponsored-content/how-much-more-private-can-zk-get-an-order-of-magnitude/
[13] https://blog.polygon.technology/introducing-polygon-id-zero-knowledge-own-your-identity-for-web3/